In Web3 Security, the Most Important Habit Is Slowing Down
Introduction: In the AI era, the easiest way to scam you is to make you move faster
Most people assume Web3 risk comes from code. In reality, most losses come from the same place: being pushed to make a decision at the exact moment you should be slowing down.
AI has made that pressure far more convincing. The profile photo looks real. The tone sounds right. The screenshot looks legitimate. The group chat feels authentic. Even the format of an “official notice” can now be replicated in seconds.
So this piece is not about theory. It is about what works.
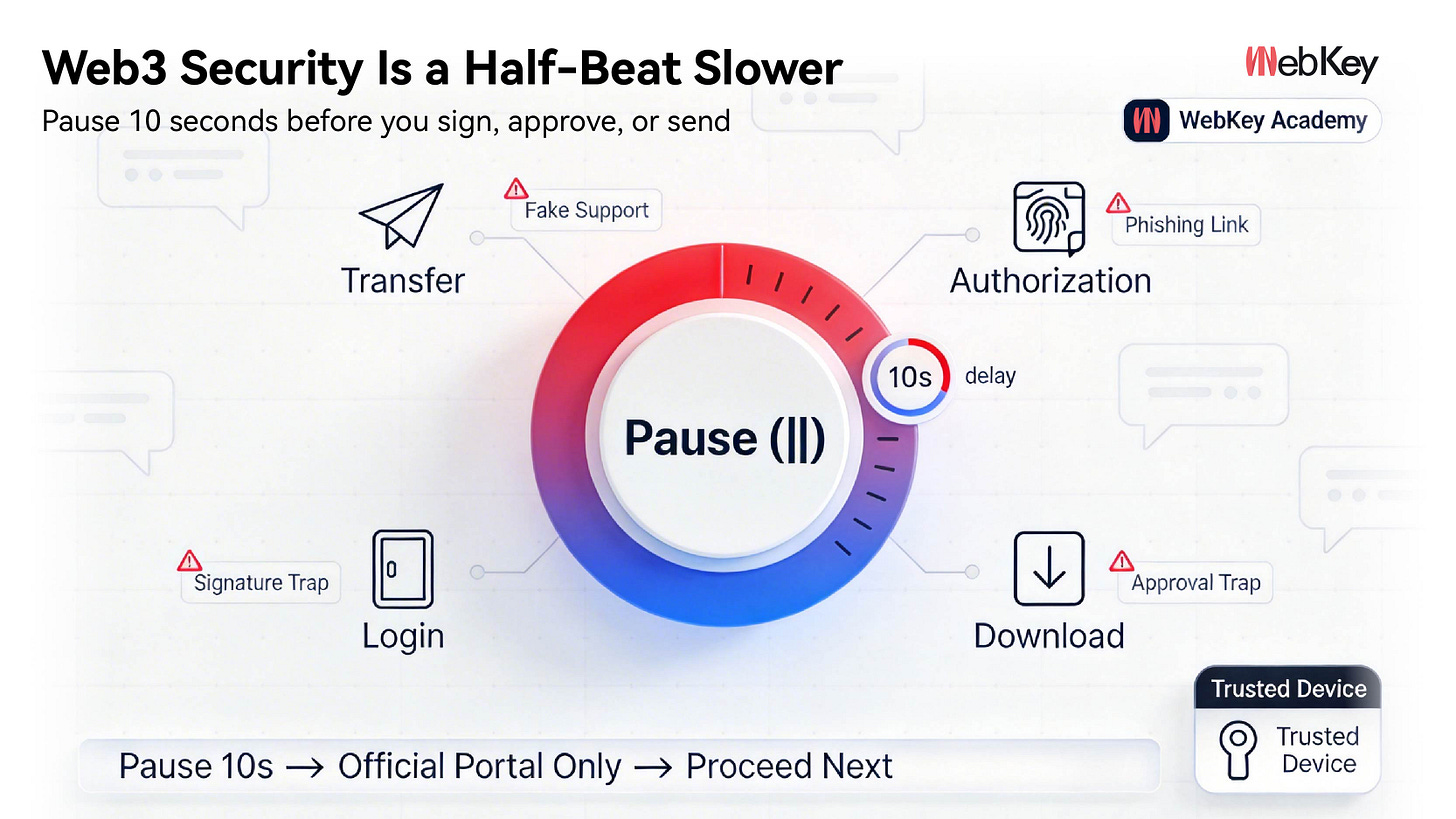
Turn security into a process, and process into habit. You do not need to stay on edge all the time. You simply need to be half a beat slower before any critical action.
I. Start with one hard rule: if someone wants you to act immediately, pause for 10 seconds
Any time an action involves one of these four things—sending funds, granting approvals, logging in, or downloading files—and the other side starts using words like:
“urgent,” “confidential,” “right now,” “expires soon,” or “your account will be frozen if you do not act,”
treat the risk level as instantly elevated.
Your default response should be three steps:
Pause for 10 seconds → use only an official channel you already know → then decide what to do next
It sounds simple, but this one habit can stop most social engineering attacks. Scammers depend on controlling your pace. The moment you stop moving on their timing, they lose their advantage.
II. The four most common scams you are likely to encounter
1) Fake support: moving you from a public channel into a private chat
Scammers are not afraid of your questions. They are afraid of you asking them through a real official channel.
The moment you are moved into a private chat, the next step is usually a link, a file, remote access, or a verification code.
Remember this: support only counts if you opened the channel yourself. If someone else sends you the entry point, do not trust it.
2) Phishing links: they look like the official site, except for one character
The most dangerous scams are not the obviously fake ones. They are the ones that look almost right.
Sometimes the difference is one extra letter, one missing dot, or a substituted character that looks nearly identical to the real one.
The safest habit is simple: use only fixed entry points saved in your bookmarks. Do not open “temporary links” sent through chat.
3) Approval traps: what looks like a login is actually a permission grant
Many pages make “confirm” feel harmless, like an ordinary login step.
But in Web3, a signature or token approval is not a formality. It can be an irreversible transfer of permission.
Your bottom line should be clear:
If you do not understand it, do not sign.
If you cannot clearly see the scope of the approval, exit.
If you are asked to approve first and claim later, treat it as a red flag.
4) Fake airdrops and fake rewards: small incentives in exchange for major permissions
“Miss it and it is gone.”
“Today only.”
“Internal whitelist.”
These lines work because they are not meant to inform you. They are meant to trigger you.
The simplest test is this: real rewards are announced through public official channels, not private messages. Anything that asks you to approve first should be treated as a risk first.
III. WebKey Academy: turning security into a trainable core skill
Real security is not about being timid. It comes from knowing exactly what you are doing—and exactly what you will never do.
Most people are not careless. They are missing a stable process. When panic takes over, instinct takes over. And instinct is exactly what scammers know how to exploit.
That is why we built WebKey Academy. The goal is straightforward: break down the most common traps in Web3, explain them clearly, and help users build real muscle memory.
1) Breaking scams down to the level of the script, so you can recognize the opening line immediately
How fake support creates urgency. How phishing links mimic official sites. How fake admins move you into private chats. How airdrop scams lure users into “just clicking once.”
These scams may look different on the surface, but underneath they all press the same buttons:
urgency, secrecy, special treatment, immediate action.
2) Explaining approvals and signatures clearly enough for you to make your own decisions
We explain, in plain language, what a signature or approval actually allows someone else to do, how to quickly assess the scope of the risk, how to revoke permissions that should no longer exist, and which interfaces are most likely to disguise dangerous actions as harmless confirmations.
You do not need to become a technical expert. But at a critical moment, you cannot afford to rely on luck.
3) Giving you a loss-mitigation sequence for when something goes wrong, so emotion does not take over
When something goes wrong, the first priority is not explanation. It is sequence:
revoke permissions first,
return to the official channel first,
move assets to a safer environment first,
then review what happened.
WebKey Academy turns that sequence into a checklist you can follow under pressure.
4) Turning good habits into short drills, so the right behavior becomes automatic
Fixed official entry points. Double checks. Wallet segmentation. Minimal approvals. Regular permission cleanup. Critical actions performed only on trusted devices.
Security is not built overnight. But once these habits are in place, your margin of safety becomes much more real.
IV. This week’s action checklist
Keep only one or two fixed official entry points in your bookmarks or pinned tabs.
Do not click links sent through private messages. Decline all remote-access requests.
Segment your assets: use a small wallet for daily activity, and a more secure setup for long-term holdings.
Review approvals once a week. Revoke anything unfamiliar or no longer needed.
Carry out critical actions only on trusted devices, never on temporary computers or unfamiliar networks.
Conclusion: Real security is not about being more anxious. It is about having a process.
Web3 offers real opportunity, but it has never rewarded carelessness.
WebKey makes trusted interaction easier. WebKey Academy makes costly mistakes less likely at the moment they matter most.
Less luck. More process. That is what real security looks like in the AI era.